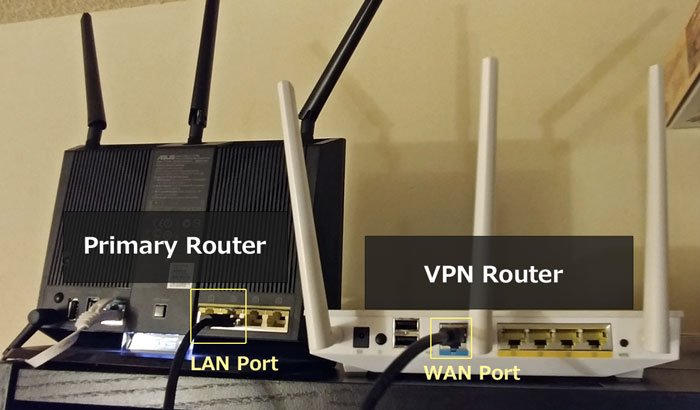
If you have an Enterprise VPN solution such as Cisco, Watchguard, Sonicwall, or others, as an end user cannot enable split-tunneling. It is managed by the VPN appliance and will require the administrator to configure and enable if they see a need to do so. When connecting using Cisco VPN, the server has to ability to instruct the client to prevent local LAN access. Assuming this server-side option cannot be turned off, how can allow local LAN access while connected with a Cisco VPN client?
- I have a Cisco ASA 5520 that has a Client Access VPN using Cisco AnyConnect. When most users connect to the VPN they have access to the office network and can still have local network access. Some users are reporting that when they connect to the VPN they lose local network access. The AnyConnect client is configured to 'Allow local (LAN.
- Unfortunately there is no checkbox to allow local LAN access via the SSL VPN client. The only way I found to enable this is to do the following: GUI. 1.) Set 'Split Tunnel Policy = Exclude Network List Below' 2.) Create an ACL to exclude the known local LAN (e.g. 192.168.0.0/16) 3.) Set 'Split Tunnel Network = CLI. Group-policy attributes.
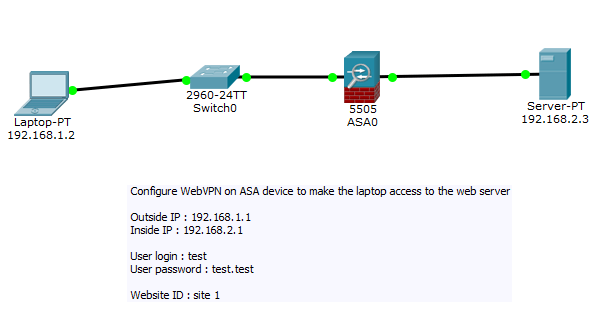
- I am stuck in a lab. My IPSec site to site VPN is working fine but I want to set up Local and Remote ID types in the IKEV1. Please guide me with commands to setup remote and local ID type. This will be same like as Fortigate or Sophos Phase 1 ID. Regards, Deepak Kumar.
William Cash and Keonwook Kang
|
Updates
4/28/09 - This guide has been around in different forms for nearly two years and has generated a good deal of interest. The basic steps are still exactly the same, but many of the compilation errors listed in the subsections have been resolved in newer versions of the Cisco VPN client (v4.8.02.0030) and Linux kernel (2.6.28). I'm still actively updating this site for my own sake, so please contact me (William Cash) with any mistakes or suggestions.
4/29/09 - Added a section on vpnc in Ubuntu, because I now feel that it's integrated into the OS well-enough to be superior to the Cisco VPN client.
Introduction
Cisco VPN is required to connect to many of Stanford's computer resources because of some past security lapses. Unlike the Windows and Mac OS clients, Cisco's Linux VPN requires use of the terminal and comparatively little documentation from the company. This guide will show you how to install and use the Linux client. In addition, it addresses some of the most common problems encountered during this problem.
As an alternative to using the Cisco VPN client, vpnc is an open-source program available on many *NIX systems that is compatible with Cisco VPNs. A general guide for vpnc is not included here. However, instructions for using it with Ubuntu's Network Manager are discussed at the end of this document. This is a more elegant and useful way to connect to Cisco VPNs, and I encourage Ubuntu users to try this before they install the Cisco VPN client.
Installing the VPN client
Note: most of the following steps require superuser access.
- Download the v4.8 VPN client from http://vpn.stanford.edu.
- Extract the downloaded file.
- Install the VPN client
- Answer the following questions during the installation (the defaults should be fine)
- Note that you need to reinstall the VPN client whenever your kernel is upgraded. Before reinstalling it, first run:
- to clean files and directories previously installed.
If you're receiving errors during installation
Most common error
With the newer Linux kernels that are incompatible with the Cisco VPN you may receive an errors similiar to these:
This is a fairly well known problem with numerous websites and forum postings on the topic. The website http://projects.tuxx-home.at has been releasing patches for the installation files of the Cisco VPN client for all the latest Linux kernels.
Instead of using the VPN client provided by Stanford, download the latest one from there (currently v4.8.02.0030) and the patch file for the linux kernel you are running. Update: Stanford has finally decided to upgrade its download to v4.8.02.0030 , as well. If you aren't sure which you have run:
Assuming you've already performed steps 1-2 of installation procedure for the new client, you will now place your patch file in the vpnclient directory and patch the installation:
Then follow steps 3 and 4 as before.
64-bit operating system errors
If you are still receiving errors after using the previous patch and are using a 64-bit OS, you should also patch the installer with cisco_skbuff_offset.patch from http://projects.tuxx-home.at.
Then follow steps 3 and 4 as before.
CFLAGS / EXTRA_CFLAGS error
Finally, if you've tried the last two patches and are receiving the following error when compiling:
you need to do exactly what the compiler error is telling you and change CFLAGS to EXTRA_CFLAGS in the makefile. First, open the file Makefile in the installer directory with your preferred text editor.
Then, change CFLAGS to EXTRA_CFLAGS in line 15. The line should read:
Now try compiling once more.
Configuring the VPN Client
Note: As an alternative to the steps below, Stanford now provides a working configuration file that can simply be placed in the Profile directory (/etc/opt/cisco-vpnclient/Profiles). A line to store your user name can be added to the profile (see Step 2). This profile is not included in the supplied VPN client and must be downloaded separately from http://vpn.stanford.edu.
- A sample configuration file is: /etc/opt/cisco-vpnclient/Profiles/sample.pcf.
- Copy and edit the configuration file.
- The edited configuration file should look similar to this:
- Start VPN service.
- Note that VPN service will be started automatically at boot time. If you want to stop VPN service, use the option stop instead. Also, You may use status, restart or reload in addition to start and stop.
- For a detailed description of each keyword in configuration file, refer to Cisco's guide.
VPN service still does not start automatically after rebooting
If you issued the previously mentioned command to start the VPN service at boot but are receiving the error message:
after rebooting, your operating system is not actually starting the service. A temporary, but somewhat annoying fix, is to continue issuing the command:
each time you reboot the system. To actually remedy the problem, you need to create symbolic links for the VPN client at different run-levels. The Cisco VPN client, only creates one in runlevel 4, but many Linux OS's don't run at this level. For example, Ubuntu commonly uses runlevel 2. To have the client start at boot for runlevel 2, issue the command:
To have the client run at a different runlevel boot simply replace rc2 in the previous command with the appropriate number. If you are unsure which runlevel to choose, you could place links in all seven.
Connecting to the VPN Host

- Once the VPN client service starts, you are ready to connect to the VPN Concentrator. Enter the group password and your SUNet ID/Pass to activate the connection. The group password is given in the file REAME-Stanford.Note: If you don't want to keep entering that terrible group password, you can store it under GroupPwd= in the configuration file. The first time the client connects with the host it will remove the plain-text password and replace it with an encrypted one under enc_GroupPwd=.
- Press ctrl + z and type bg to run vpnclient in the background. Now you can do ssh or scp to other machines.
- To disconnect, type:
If you are unable to connect without superuser privileges
When trying to connect to the VPN host as a regular user you may encounter the following error:
This is because you don't have the correct privileges to read the profile file.
To change its permissions run:
as the superuser.If you are still not able to use the VPN without being root, type:
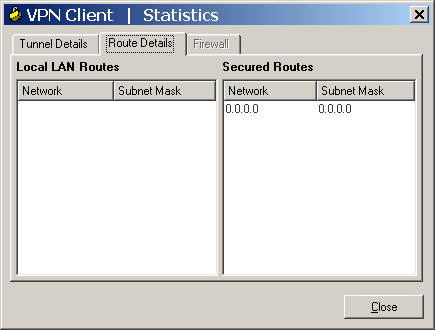
If you are unable to browse the internet, check email, etc. after connecting to the VPN
Cisco Vpn Local Lan Access
Another common problem with the Cisco VPN client for linux is that it disables your local LAN access once you connect to the host, even if the host is not set to disable local LAN access. This can be remedied with the override-local-lan-access.diff patch from projects.tuxx-home.at. You will first have to uninstall your VPN client and move the patch to vpnclient source code directory. If you had to use the aforementioned kernel patch, apply that first. Then apply the LAN access patch and install as usual.
Additional LAN access issues due to Firestarter firewall
Firestarter is a popular desktop firewall tool used by many Linux users. However, it can also restrict internet access when the Cisco VPN is active. A quick temporary fix is to open the Firestarter utility and simply stop the firewall. A safer and permanent fix is to add the following code to /etc/firestarter/user-pre (for many users this file will be empty beforehand):
Where xxx.xxx.xxx.xxx is the IP address of the VPN server (you can find this from the Server Address given when starting the VPN), and cipsec0 is the common name for the VPN network device on your computer. You can verify if cipsec0 is the correct name by running:
ifconfig will also display the names of your network and/or wireless cards.
For the changes to take effect, you will need to restart the firewall by running:
vpnc Integration with Network Manager in Ubuntu 9.04
Ubuntu's Network Manager is the way Ubuntu organizes all your wired and wireless networks. It's the icon in the task bar you're always clicking to view all the available wifi signals, because it always seems to connect to the wrong network. It used to suck (e.g. 7.04), but it has improved greatly in recent releases. In version 9.04, I finally feel that it is reliable enough to warrant a section in this guide - especially since more of us at Stanford seem to be using Ubuntu these days.
Cisco Vpn Allow Local Lan Access
- To allow Network Manager to manage your Cisco VPN connection you will first need to install the vpnc plugin. You will need to get the packages network-manager-vpnc and vpnc from the Ubuntu repositories using either the Synaptic Package Manager or apt-get. If this is over your head, you can also find it in Add/Remove Programs if you search for 'vpnc' in all available applications.
- Click the Network Manager icon in your task bar and there should now be an option labeled 'VPN Connections'. Expand this option and select Configure VPN, as shown below (my desktop and task bar probably look different than yours because I was on my netbook).
- The Network Connections window should open with the VPN tab selected. Choose the 'Add' option to create a new VPN connection, or you can import an existing .pcf configuration file using the 'Import' button. A window like the one below will open. Gateway is the URL or IP address of the VPN host (this is called 'Host' in the Cisco .pcf configuration file). Group name, user name, and their passwords are all self-explanatory and can be permanently stored if you prefer. These should be the only options most users should have to change.
- Apply the changes and now try to connect to the VPN by returning to Network Manager in the task bar and selecting your newly created VPN.Stanfprd _Public_VPN .pcf configuration file
- It may ask you for access to your network security key ring. You should select 'Always Allow' unless you want the window to continually pop up.
- If it successfully finds the server it will either ask or verify your passwords. Assuming these are correct you should receive a confirmation message such as the one below. I'm not sure if this message is specific to the Stanford VPN, but it asks you to click the 'Continue Button'. I have no idea where this so-called button is, but the VPN works fine anyway. You will know your VPN connection is active if there is a gold padlock on top of your Network Manager icon.
- Actually, Stanford offers a very convenient way to set the VPN parameter in Ubuntu. After installing the packages vpnc, network-manager-vpnc and network-manager-vpnc-gnome, you can directly download the Stanford _Public_VPN .pcf configuration file from https://itservices.stanford.edu/service/vpn/downloads. Next, you should select VPN Connections > Configure VPN from the GNOME notification area and import the .pcf file you have downloaded. Finally, you may edit this VPN connection configuration by entering your SUNet ID in the User name field and entering your SUNet password in the password field.
Cisco Vpn Local Lan Access When Using Vpn
References
Cisco Anyconnect Vpn Client Download
How can I maintain local LAN access while connected to Cisco VPN?
When connecting using Cisco VPN, the server has to ability to instruct the client to prevent local LAN access.
Assuming this server-side option cannot be turned off, how can allow local LAN access while connected with a Cisco VPN client?
I used to think it was simply a matter of routes being added that capture LAN traffic with a higher metric, for example:
And trying to delete the 10.0.x.x -> 192.168.199.12 route don't have any effect:
And while it still might simply be a routing issue, attempts to add or delete routes fail.
Enable Local Lan Access
At what level is Cisco VPN client driver doing what in the networking stack that takes overrides a local administrator's ability to administer their machine?
The Cisco VPN client cannot be employing magic. It's still software running on my computer. What mechanism is it using to interfere with my machine's network? What happens when an IP/ICMP packet arrives on the network? Where in the networking stack is the packet getting eaten?
See also
Edit: Things I've not yet tried:
Free Cisco Vpn Anyconnect Download
Update: Since Cisco has abandoned their old client, in favor of AnyConnect (HTTP SSL based VPN), this question, unsolved, can be left as a relic of history.
Cisco Vpn Local Lan Access Not Working
Going forward, we can try to solve the same problem with their new client.
